1、说明
所需软件及下载地址
CentOS 5.2----------------------------------***稳定的linux服务器
ppp-2.4.3.tar.gz----------------------------PPP主程序
openssl-0.9.8i.tar.gz-----------------------生产证书的主程序
xl2tpd-1.2.3.tar.gz-------------------------FreeRadius服务器主程序
openswan-2.6.19.tar.gz----------------------IPSec主程序
1.2、实现过程及功能特性
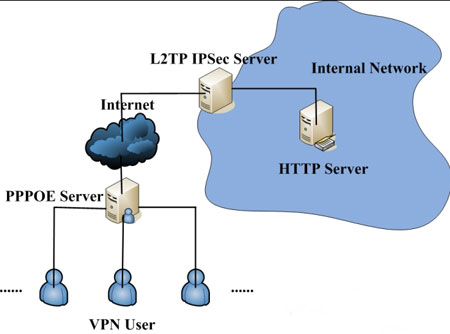
我们的试验网络拓扑如下图所示:
我们采用VM虚拟机试验,VM中的网络设置如下:
在VMware提供的Virtual Network Editor中的“Host Virtual Network Mapping”选项卡中,把VMNet2设为Not bridged,点击右边的“>”按钮-subnet,IP地址填入172.16.1.0,确定。
VPNGateway虚拟机需要再添加一个网卡,然后在Linux下按照下表设置各个网卡,并在虚拟机设置中选择网卡对应的网络。其中VPNGateway的网卡0属于VMNet0,网卡1属于VMNet2。网卡1的默认网卡设为192.168.2.1。
另外,XP本机自动位于VMNet0,不需要进行设置。

其中,192.168.1.0/24网段模拟外网,windows xp模拟外网拨号的VPN客户机。
172.16.1.0/24网段模拟内网,Juniper为内网中一台机器,作为企业内部的HTTP服务器。
2.架设服务器
具体过程不再赘述,相关配置文件如下:
OpenSWan 主要配置文件:
/etc/ipsec.secrets 用来保存private RSA keys 和 preshared secrets (PSKs)
/etc/ipsec.conf 配置文件(settings, options, defaults, connections)
OpenSWan 主要配置目录 :
/etc/ipsec.d/cacerts 存放X.509 认证证书(根证书-"root certificates")
/etc/ipsec.d/certs 存放X.509 客户端证书(X.509 client Certificates)
/etc/ipsec.d/private 存放X.509 认证私钥(X.509 Certificate private keys)
/etc/ipsec.d/crls 存放X.509 证书撤消列表(X.509 Certificate Revocation Lists)
/etc/ipsec.d/ocspcerts 存放X.500 OCSP 证书(Online Certificate Status Protocol certificates)
/etc/ipsec.d/passwd XAUTH 密码文件(XAUTH password file)
/etc/ipsec.d/policies 存放Opportunistic Encryption 策略组(The Opportunistic Encryption policy groups)
[root@mm ~]# cat /etc/ppp/chap-secrets # Secrets for authentication using CHAP #
client server secret IP addresses
test1 * test1 *
l2tptest1 * l2tptest1 10.1.1.1
l2tptest2 * l2tptest2 *
[root@mm ~]# cat /etc/ipsec.secrets
RSA /etc/ipsec.d/private/vpngateway.key "123456"
#192.168.1.251 %any : PSK "123456"
[root@mm ~]# cat /etc/ipsec.conf
#version 2.0
config setup
interfaces=%defaultroute
nat_traversal=yes
virtual_private=%v4:192.168.0.0/16,%v4:10.0.0.0/8,%v4:172.16.1.0/24,%v4:!192.168.1.0/24
conn %default
compress=yes
authby=rsasig
leftrsasigkey=%cert
rightrsasigkey=%cert
#conn roadwarrior
#left=172.16.1.100
#leftcert=vpngateway.cert
#leftsubnet=172.16.1.0/24
#right=%any
#auto=add
conn l2tpx509
pfs=no auto=add
left=192.168.1.251
leftcert=vpngateway.cert
leftprotoport=17/1701
right=%any
rightca=%same
rightprotoport=17/%any ############################################################################# #configure preshared secret authentication
#conn l2tp
# authby=secret
# pfs=no
# auto=add
# type=transport
# left=192.168.1.251
# leftprotoport=17/1701
# right=%any
# rightprotoport=17/%any ############################################################################# #include /etc/ipsec.d/examples/no_oe.conf
[root@mm ~]# cat /etc/ppp/options.xl2tpd
ipcp-accept-local
ipcp-accept-remote
ms-dns 192.168.10.1
ms-dns 192.168.10.3
ms-wins 192.168.10.2
ms-wins 192.168.10.4
#noccp
auth
crtscts
idle 1800
mtu 1410
mru 1410
nodefaultroute
debug
lock
proxyarp
connect-delay 5000
logfile /var/log/l2tpd.log
proxyarp
[root@mm ~]# cat /etc/xl2tpd/xl2tpd.conf
[global]
listen-addr = 192.168.1.251
port = 1701
auth file = /etc/ppp/chap-secrets
debug tunnel = yes
[lns default]
ip range = 172.16.1.10-172.16.1.254
local ip = 192.168.1.251
require chap = yes
refuse pap = yes
require authentication = yes
name = mm's L2TP VPN Server
ppp debug = yes
pppoptfile = /etc/ppp/options.xl2tpd
length bit = yes
复制证书(在机器之间复制证书请确保安全性):
#cp cacert.pem /etc/ipsec.d/cacerts
#cp vpngateway.cert /etc/ipsec.d/certs
#cp vpngateway.key /etc/ipsec.d/private
#cp crl.pem /etc/ipsec.d/crls/
CA工作目录: /root/CA
# openssl req ‐x509 ‐days 3650 ‐newkey rsa:1024 ‐keyout cakey.pem ‐out cacert.pem
# mkdir newcerts
# touch index.txt
# echo "01" > serial
# echo "01" > crlnumber
# mkdir private
# cp cakey.pem ./private/
# openssl ca ‐gencrl ‐out crl.pem
# openssl req ‐newkey rsa:1024 ‐keyout vpngateway.key ‐out vpngatewayreq.pem
# openssl ca ‐in ../vpngatewayreq.pem ‐days 365 ‐out ../vpngateway.cert ‐notext
# openssl pkcs12 ‐export ‐in cacert.pem ‐inkey cakey.pem ‐out demoCA.p12
下面产生windows的私钥及证书:
# openssl req ‐newkey rsa:1024 ‐keyout windows.key ‐out windowsreq.pem
# openssl ca ‐in ../windowsreq.pem ‐days 3650 ‐out ../windows.cert ‐notext
# openssl pkcs12 ‐export ‐in windows.cert ‐inkey windows.key ‐out windows.p12
注意,在导出P12文件时,输入读取CA密钥的密码,然后再指定导出p12文件中的证书需要
的密码,并进行二次确认。
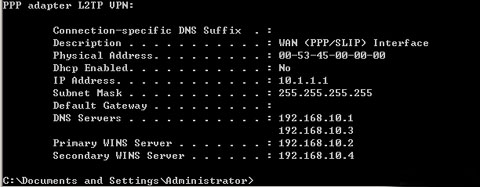
用户名l2tptest1,密码l2tptest1,进行拨号,
可以看到获得的IP 是/etc/ppp/chap‐secrets 文件中指定的那个IP:

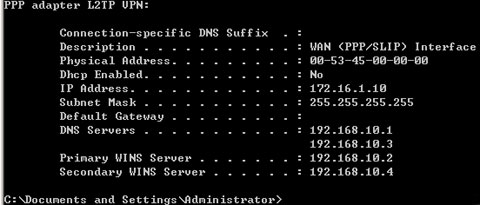
用户名l2tptest2,密码l2tptest2,进行拨号,
可以看到获得的IP 是从地址池中获得的:
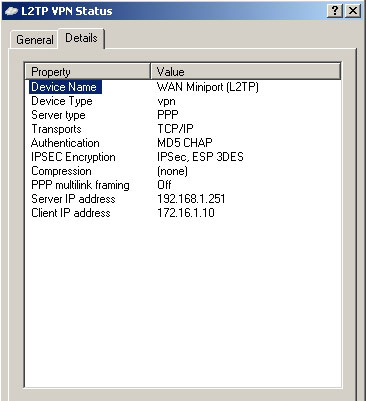
一个完整的拨号连接信息如下:
xl2tpd[7581]: build_fdset: closing down tunnel 34285
xl2tpd[7581]: get_call: allocating new tunnel for host 192.168.1.55, port 1701.
xl2tpd[7581]: get_call: allocating new tunnel for host 192.168.1.55, port 1701.
xl2tpd[7581]: control_finish: Peer requested tunnel 3 twice, ignoring second one.
xl2tpd[7581]: build_fdset: closing down tunnel 46042
xl2tpd[7581]: Connection established to 192.168.1.55, 1701. Local: 26849, Remote: 3 (ref=0/0).
LNS session is 'default'
xl2tpd[7581]: start_pppd: I'm running:
xl2tpd[7581]: "/usr/sbin/pppd"
xl2tpd[7581]: "passive"
xl2tpd[7581]: "‐detach"
xl2tpd[7581]: "192.168.1.251:172.16.1.10"
xl2tpd[7581]: "refuse‐pap"
xl2tpd[7581]: "auth"
xl2tpd[7581]: "require‐chap"
xl2tpd[7581]: "name"
xl2tpd[7581]: "mm's L2TP VPN Server"
xl2tpd[7581]: "debug"
xl2tpd[7581]: "file"
xl2tpd[7581]: "/etc/ppp/options.xl2tpd"
xl2tpd[7581]: "/dev/pts/1"
xl2tpd[7581]: Call established with 192.168.1.55, Local: 64654, Remote: 1, Serial: 0
xl2tpd[7581]: network_thread: select timeout
xl2tpd[7581]: network_thread: select timeout
xl2tpd[7581]: child_handler : pppd exited for call 1 with code 10
xl2tpd[7581]: call_close: Call 64654 to 192.168.1.55 disconnected
xl2tpd[7581]: control_finish: Connection closed to 192.168.1.55, port 1701 (), Local: 26849,
Remote: 3
xl2tpd[7581]: build_fdset: closing down tunnel 26849
xl2tpd[7581]: Trustingly terminating pppd: sending TERM signal to pid 7633
xl2tpd[7581]: pppd 7633 successfully terminated
关于L2TP IPSec VPN 服务器的架设,暂且学习到这里,其中还有很多细节需要学习和熟悉,有待进一步的研究。



